Container Image Mirroring: Eliminating External Registry Dependencies
Relying on public registries in production creates fragile architectural bottlenecks. Here is why local image mirroring is non-negotiable for enterprise infrastructure stability.
The Invisible Fragility of “Default” Settings
For years, Bitnami has been the industry benchmark for Kubernetes charts. Commands like helm install bitnami/redis are the “easy button” for deploying infrastructure. However, this convenience masks a dangerous architectural flaw: the loss of operational sovereignty.
When you use default upstream images, you aren’t just using a tool; you are outsourcing a critical piece of your uptime to a third-party entity you do not control.
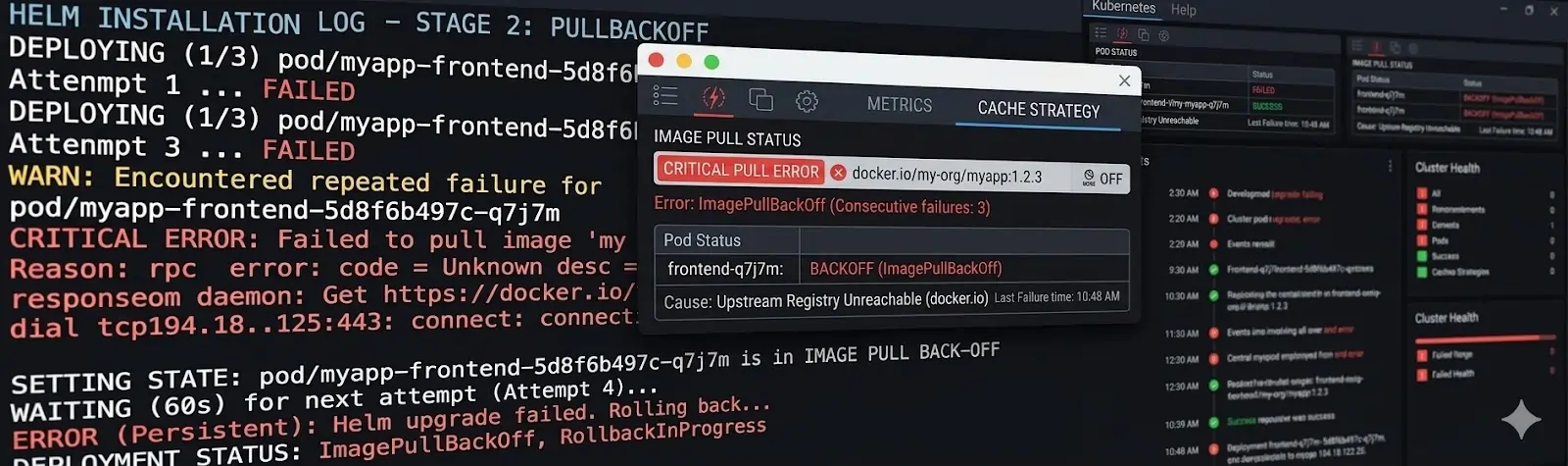
Visualizing the Operational Risk
The diagram below illustrates the fragility of depending on an external, unpredictable environment (the “Breaking World”) versus the stability of an insulated local architecture.
 Figure 1: Architectural comparison. The left path shows a stable production cluster utilizing a local Harbor registry. The right path shows the ‘Breaking World’ of external registry risks.
Figure 1: Architectural comparison. The left path shows a stable production cluster utilizing a local Harbor registry. The right path shows the ‘Breaking World’ of external registry risks.
The Cost of Upstream Volatility
The tech landscape is shifting. Acquisitions—like Broadcom’s takeover of VMware/Bitnami—frequently result in altered image paths, modified versioning schemes, and migrated repositories.
In a local dev environment, a broken image path is a 10-minute annoyance. In a production CI/CD pipeline, it is a deployment blocker.
The Failure of Implicit Trust
Modern infrastructure must be immutable. If your cluster needs to scale during a traffic surge, but the external registry is hitting rate limits or has deprecated your specific tag, your auto-scaler fails. Your internal reliability should never be a hostage to an external file path.
The Solution: Local Image Mirroring
To achieve production-grade resilience, organizations must decouple their clusters from the public internet. Local mirroring isn’t just a backup; it’s a strategic buffer.
Why Mirroring is Mandatory:
| Benefit | Impact |
|---|---|
| Sovereign Availability | Protects against upstream outages, registry sunsets, or “deletions.” |
| Supply Chain Security | Enables automated vulnerability scanning before images reach the node. |
| Deterministic Performance | Eliminates public rate-limiting and reduces latency. |
| Cost Control | Drastically reduces egress fees by pulling from a local cache. |
Engineering a Robust Registry Strategy
We recommend treating an internal registry (like Harbor) as a Tier-0 infrastructure component.
1. Pull-Through Caching
Configure your registry to proxy upstream sources. This ensures that the moment an image is pulled once, a permanent, immutable copy is stored within your perimeter.
2. Explicit Registry Overrides
Never rely on a chart’s default values. Use the global.imageRegistry parameter in your values.yaml:
# Example: Redirecting all Bitnami images to your internal Harbor
global:
imageRegistry: registry.internal.company.com
imagePullSecrets:
- name: harbor-credentials3. Namespace Isolation
Organize your mirrored images by project or environment. This prevents “dependency drift” where different teams are pulling conflicting versions of the same base image.
Conclusion: Take Back Control
Infrastructure independence is the hallmark of a mature DevOps culture. By mirroring your container images, you transform a fragile external dependency into a robust, controlled asset.
Don’t wait for the next registry outage to realize your cluster is stranded.
Looking to harden your Kubernetes supply chain? Would you like me to draft a sample values.yaml file for a specific Helm chart to show you how to redirect these image paths correctly?